

Wasn’t Huawei trying to put a Backdoor into linux?
as far as i know, that has not happened.
what makes you think it did?
cultural reviewer and dabbler in stylistic premonitions


Wasn’t Huawei trying to put a Backdoor into linux?
as far as i know, that has not happened.
what makes you think it did?


fremdscham++ 😬


Or you could just… learn to use the modern internet that 60% of internet traffic uses? Not everyone has a dedicated IPv4 anymore, we are in the days of mobile networks and CGNAT. IPv4 exhaustion is here today.
Where are you getting 60%? Google’s IPv6 Adoption page has it under 50% still:
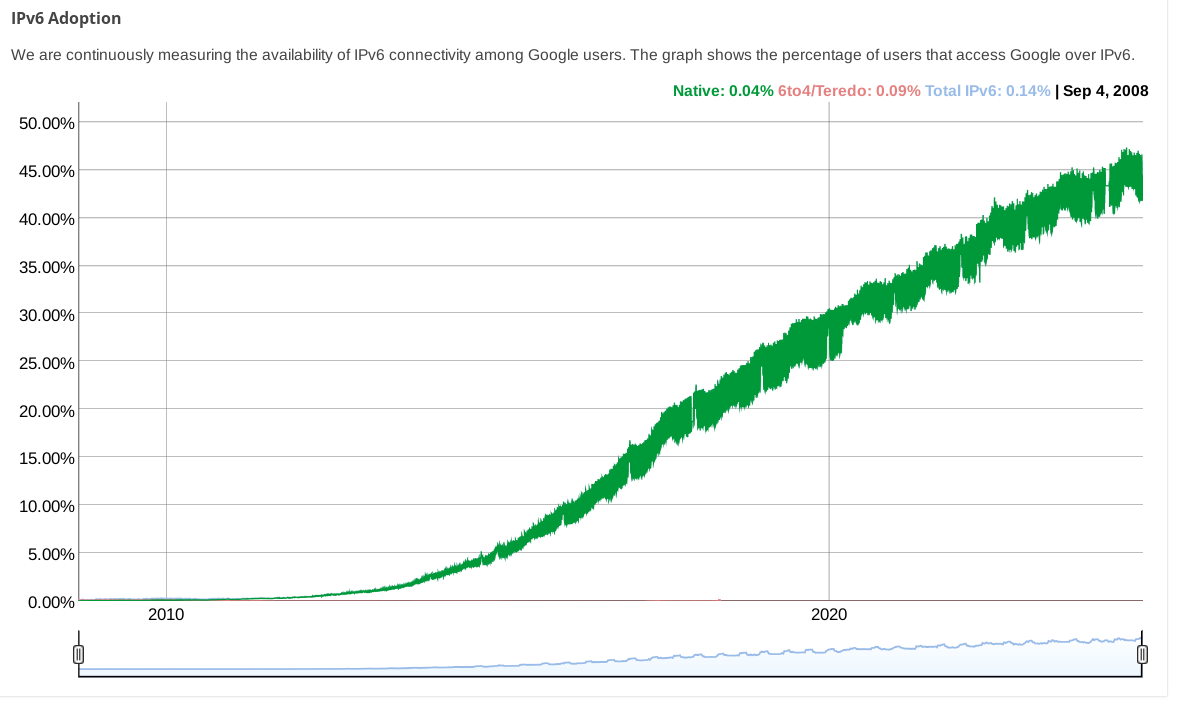
(while other stats pages from big CDNs show even less)


If you have ::/0 in your AllowedIPs and v6 connections are bypassing your VPN, that is strange.
What does ip route get 2a00:1450:400f:801::200e (an IPv6 address for google) say?
I haven’t used wireguard with NetworkManager, but using wg-quick it certainly adds a default v6 route when you have ::/0 in AllowedIPs.


You could edit your configuration to change the wireguard connection’s AllowedIPs from 0.0.0.0/0 to 0.0.0.0/0,::/0 so that IPv6 traffic is routed over it. Regardless of if your wireguard endpoint actually supports it, this will at least stop IPv6 traffic from leaking.


ipv4 with an extra octet
that was proposed as “IPv4.1” on April 1, 2011: https://web.archive.org/web/20110404094446/http://packetlife.net/blog/2011/apr/1/alternative-ipv6-works/


This video is full of jarring edits which initially made me wonder if someone had cut out words or phrases to create an abbreviated version. But, then I realized there are way too many of them to have been done manually. I checked the full original video and from the few edits i manually checked it seems like it is just inconsequential pauses etc that were removed: for instance, when Linus says “the other side of that picture” in the original there is an extra “p” sound which is removed here.
Yet another irritating and unnecessary application of neural networks, I guess.
To answer your question: yes, YTA 🤦
Also, I’m deleting this post per asklemmy rule 3.


The tone which comes across in the video (linked from the other post I linked to in this post’s description) is unfortunately much less amicable than this article conveys.


the guy speaking off camera in the linked 3min 30s of the video is Ted Ts’o, according to this report about the session.


It looks like Framework only offers entry-level Radeon GPUs.
If you want to do GPU compute in a laptop and money is no object, something from Lenovo’s Legion series of gaming laptops is probably a good choice. You can get one with an RTX 4090 in it, and the series (or many models of it, at least) appears to have reasonably good Linux support. (Disclaimer: I’ve never used one.)


i think /c/politics@lemmy.ml was removed due to redundancy with /c/worldnews@lemmy.ml more than /c/usa@lemmy.ml.
that’s not to say it couldn’t be a place for non-news-related political discussions, but in practice it mostly got posts which would fit in worldnews.
it could be restored if one or more users with a good history wants to take responsibility for moderating it.
If you’re interested in using something other than Microsoft Windows, getgnulinux.org is a good place to read about your options and how to switch.




E: old thinkpad gang input: take the time to reapply thermal grease to the cpu at some point. It makes a huge difference.
What’s a “gang input”?
😂 it’s an input to this discussion from a member of the group of people (“gang”) who have experience with old thinkpads. and yes, if your old thinkpad (or other laptop) is overheating and crashing, reapplying the thermal paste is a good next step after cleaning the fans.


xzbot from Anthony Weems enables to patch the corrupted liblzma to change the private key used to compare it to the signed ssh certificate, so adding this to your instructions might enable me to demonstrate sshing into the VM :)
Fun :)
Btw, instead of installing individual vulnerable debs as those kali instructions I linked to earlier suggest, you could also point debootstrap at the snapshot service so that you get a complete system with everything as it would’ve been in late March and then run that in a VM… or in a container. You can find various instructions for creating containers and VMs using debootstrap (eg, this one which tells you how to run a container with systemd-nspawn; but you could also do it with podman or docker or lxc). When the instructions tell you to run debootstrap, you just want to specify a snapshot URL like https://snapshot.debian.org/archive/debian/20240325T212344Z/ in place of the usual Debian repository url (typically https://deb.debian.org/debian/).


A daily ISO of Debian testing or Ubuntu 24.04 (noble) beta from prior to the first week of April would be easiest, but those aren’t archived anywhere that I know of. It didn’t make it in to any stable releases of any Debian-based distros.
But even when you have a vulnerable system running sshd in a vulnerable configuration, you can’t fully demo the backdoor because it requires the attacker to authenticate with their private key (which has not been revealed).
But, if you just want to run it and observe the sshd slowness that caused the backdoor to be discovered, here are instructions for installing the vulnerable liblzma deb from snapshot.debian.org.
Funny that blog calls it a “failed attempt at a backdoor” while neglecting to mention that the grsec post (which it does link to and acknowledges is the source of the story) had been updated months prior to explicitly refute that characterization: